Security teams are caught between a rapidly expanding attack surface and accelerating adversarial use of AI. Thirty-two percent of security teams see automated, AI-fueled attacks as the single greatest driver reshaping their offensive security strategies.
Featured
This week: How AI is reshaping security vendor business models, disrupting cybersecurity procurement, exposing governance gaps, fueling new trust debates, and further complicating persistent threats like ransomware and Microsoft insecurity.
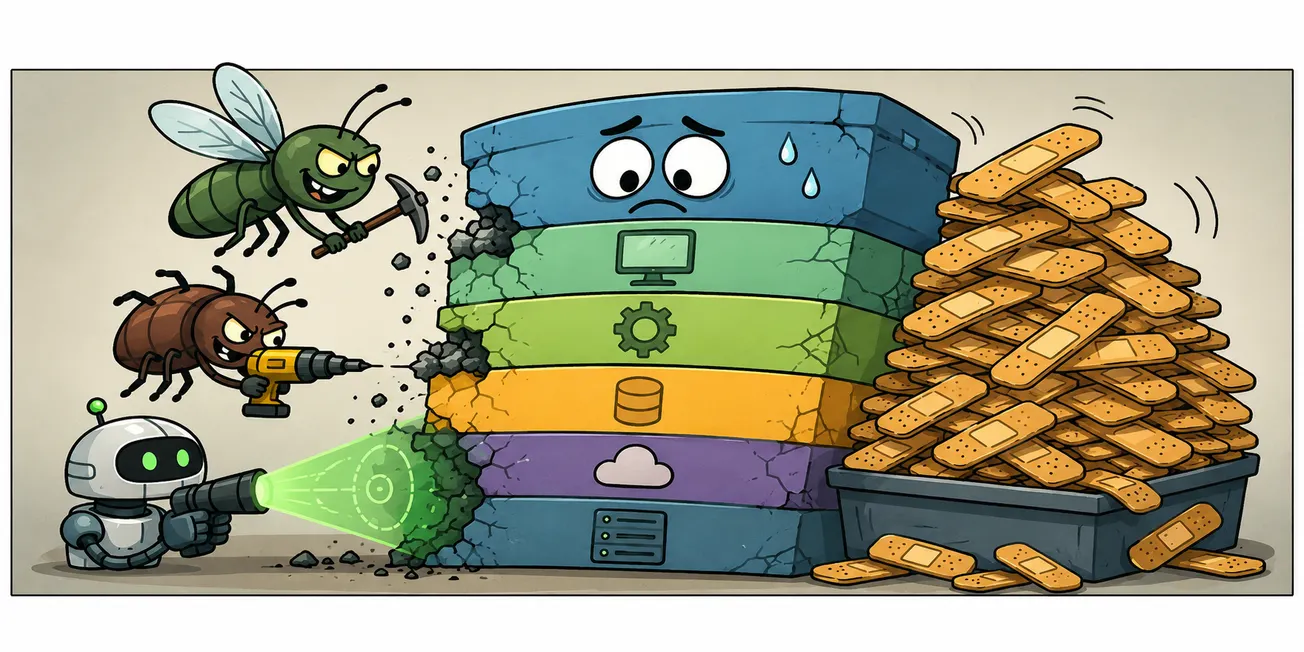
A trio of fresh flaws highlights the heightened vulnerability of the entire enterprise software stack, as the combination of automated scanning, the availability of exploit code, and patching delays is cited as a factor in the rise of vulnerability exploitation as a preferred entry point.
Community Corner
See allFrom the CYBR.SEC.Community

Trust Is Not a Cloud Service: What Cybersecurity Can Learn from Local AI Stewards
The people on the ground often know whether that event is ordinary, suspicious, urgent, harmless, political, embarrassing, dangerous, or simply the latest chapter in a long operational story.

In Appreciation: Dr. Eric Cole
Dr. Eric Cole's cybersecurity accomplishments are legendary, but his willingness to speak openly about burnout is something that particularly resonated with me, as it is something many of us struggle to avoid.

He Wasn't a Hacker. But He Was One of Us.
Thirty years after Sean Marley died, I realize that my focus on mental health in cybersecurity started with him. This is a belated thank you to him for helping me strive for something better. He wasn't a hacker. But he sure as hell was one of us.
CYBR.SEC.Media 2.0: How CYBR.SEC.Community Is Building a More Human Cybersecurity Media Platform
The new version of CYBR.SEC.Media puts community voices, practitioner insight, podcasts, videos, and visual storytelling front and center.

The Vulnpocalypse Isn’t Your Problem
But it might be your company’s problem.
Latest Articles
See all GRC
GRC
AI Governance Is Becoming Cybersecurity's Next Compliance Theater
A new report from Cye finds that AI adoption is racing ahead of AI security, leaving organizations stuck between governance policies on paper and operational controls that can actually reduce risk. The report analyzed more than 2,400 assessments across 21 countries and 16 industries.
 security vendors
security vendors
The Coming Security Vendor Identity Crisis
As AI accelerates product development and cybersecurity categories blur together, security leaders face a growing challenge: figuring out who actually does what anymore. (Sponsored by Crush Security.)
 ProcurementVARSAgentic AI
ProcurementVARSAgentic AI
The VAR Model Is Broken. Can AI Finally Fix Cybersecurity Procurement?
Security leaders have spent years optimizing detection and response while relying on spreadsheets, tribal knowledge, and reseller relationships to make million-dollar technology decisions. A new generation of AI-powered platforms aims to change that. (Sponsored by Crush Security.)
 RansomwareOT Cybersecurity
RansomwareOT Cybersecurity
Industrial Ransomware Held Steady in Q1 2026, That's the Problem
The normalization of ransomware in industrial systems, along with an operating culture that treats downtime as unacceptable, is an uncomfortable tension that's not likely to go away soon.
 Microsoft Security
Microsoft Security
Four YouTube Influencers Decode Microsoft's 'Nightmare Eclipse' Dumpster Fire
This week, we recognize four cybersecurity influencers on YouTube who skillfully unpacked the war between Microsoft and "Nightmare Eclipse."
 zero trustAgentic AIIdentity Security
zero trustAgentic AIIdentity Security
Agentic AI Is Pushing Zero Trust Into Its Next Phase
Zero Trust was designed to control people and machines. The rise of autonomous AI agents is forcing security teams to extend those same principles to software capable of making decisions and taking action on its own. (Includes infographic)
 Identity SecuritySaaS
Identity SecuritySaaS
After the Vishing Call: What Enterprises, SaaS Providers, and Salesforce Need to Do Differently
Salesforce knew its platform was being systematically exploited. Charter's customers are paying the price. The gaps that enabled these intrusions are largely the same. Here's what enterprises and platform providers should have done and still need to do.
Podcasts & Video
See all Podcast
Podcast
CYBR.SEC.CAST Episode 69: Crush Security
We are joined by Crush Security co-founders Joshua Jones and Josh Johnson, plus CISO John Barrow. They discuss navigating an increasingly complex vendor ecosystem where tool sprawl, contract complexity, reseller incentives, and budget pressure make buying harder. (Sponsored by Crush Security)
 Podcast
Podcast
CYBR.HAK.CAST Episode 14: Tim Medin
In this episode, hosts Michael Farnum and Phillip Wylie sit down with penetration tester and Red Siege founder Tim Medin to talk about turning attacker tactics into practical defensive wins.
 Video
Video
OT Resilience in Action: A Framework for Utilities
 Podcast
Podcast
CYBR.HAK.CAST Episode 13: Winn Schwartau
Winn Schwartau argues that the biggest threat facing defenders isn’t just technical, but cognitive: overwhelming information flows that push humans into “mental DDoS.” He has introduced the concept of “critical ignoring” as a prerequisite to critical thinking.
 Video
Video
Enhancing OT Cybersecurity in Maritime Environments
 Video
Video
The Executive Imperative: Acting Decisively When You Need to Defend OT
 Video
Video