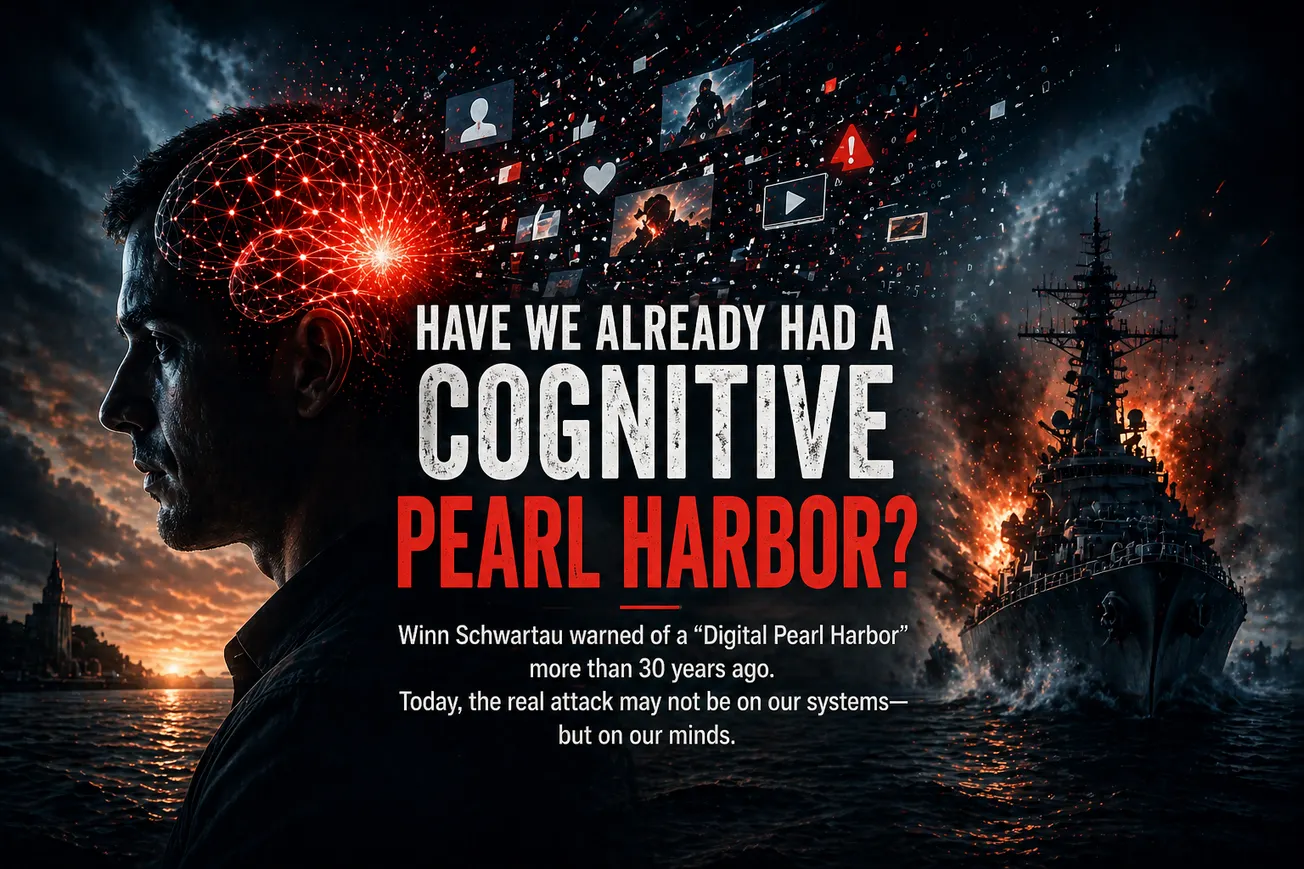
This episode of CYBR.HAK.CAST features Winn Schwartau in a wide-ranging, philosophical discussion that moves from the early, experimental days of cybersecurity to today’s hyper-commercialized landscape—and into his current work on “cognitive security.” Schwartau argues that the biggest threat facing defenders isn’t just technical, but cognitive: overwhelming information flows that push humans into “mental DDoS.” He introduces the concept of “critical ignoring” as a prerequisite to critical thinking, framing cybersecurity, biology, and human cognition as interconnected systems governed by OODA loops. The conversation culminates in a provocative question: are we already experiencing a “cognitive Pearl Harbor,” where belief systems – not infrastructure – are the true attack surface?
SHOW NOTES:
Things Mentioned:
- Winn's website: https://www.winnschwartau.com/
- The Cognitive Security Institute: https://www.cognitivesecurityinstitute.org/
- Upcoming CYBR.SEC.Community events: https://www.cybrsecmedia.com/conference/
- CYBR.SEC.Careers: https://www.linkedin.com/company/cybr-sec-careers/about/ fundraisers:
Episode 13 Timestamps:
00:00 – 06:00 — Intro + Community updates
Hosts (Michael Farnham, Philip Wiley) open with banter and promote CyberHackCon, speakers, and CyberSecCareers nonprofit workforce initiatives.
06:00 – 14:00 — Schwartau’s origin story
From fixing TVs as a kid to early work in computing and security in the 1980s. Emphasis on “tabula rasa” era—no rules, everything experimental.
14:00 – 20:00 — Early cybersecurity vs. today
Discussion on how innovation has been constrained by VC pressure, commercialization, and loss of “garage-level” experimentation.
20:00 – 28:00 — Transition to cognitive security
Schwartau explains his shift from traditional cybersecurity to studying cognition, neurophysics, and system-level survival models.
28:00 – 40:00 — “Critical ignoring” vs. critical thinking
Core thesis: humans cannot process all incoming information. Filtering (ignoring) must come before analysis, or we enter cognitive overload (“mental DDoS”).
40:00 – 50:00 — Parallels to SOC operations
Hosts connect ideas to alert fatigue and AI-driven SOC tooling—reducing noise to enable meaningful analysis.
50:00 – 60:00 — OODA loops and time-based reality
Everything—cyber, biology, cognition—operates in delayed reaction loops. We are always reacting to the past.
60:00 – 70:00 — Cognitive overload and misinformation
Exploration of disinformation, narrative formation, and limits of human processing in modern environments.
70:00 – End — “Cognitive Pearl Harbor”
Schwartau poses the central question: has a large-scale cognitive attack already occurred? Discussion spans individual, enterprise, and societal levels.
Do you have a question for the hosts? Reach out to us at media@cscgroupllc.com
Keep up with CYBR.SEC.CON.:
Keep up with CYBR.SEC.Media:
Check out our Conferences and Events:
Support or apply to our Scholarship Program:
Subscribe to the podcast:
In this episode:
- Host: Michael Farnum
- Host: Phillip Wylie
- Guest: Winn Shwartau
- Production and editing: Lauren Andrus
- Music by: August Honey