In this article:
- How Schwartau’s “Electronic Pearl Harbor” concept has evolved
- Why belief systems are now the primary attack surface
- What a “cognitive Pearl Harbor” actually looks like
In the early 1990s, Winn Schwartau warned of a “Digital Pearl Harbor”— a devastating cyberattack on infrastructure.
Now, he’s asking a different question – not about systems, but about us:
“Have we become part of a cognitive Pearl Harbor?”
The question is a challenge that – in the context of today’s AI-driven information environment – lands closer to reality than most security teams are comfortable admitting. It's also a complex issue to unpack.
Watch or listen to the full CYBR.HAK.CAST episode with Winn:

The problem isn’t just bad information
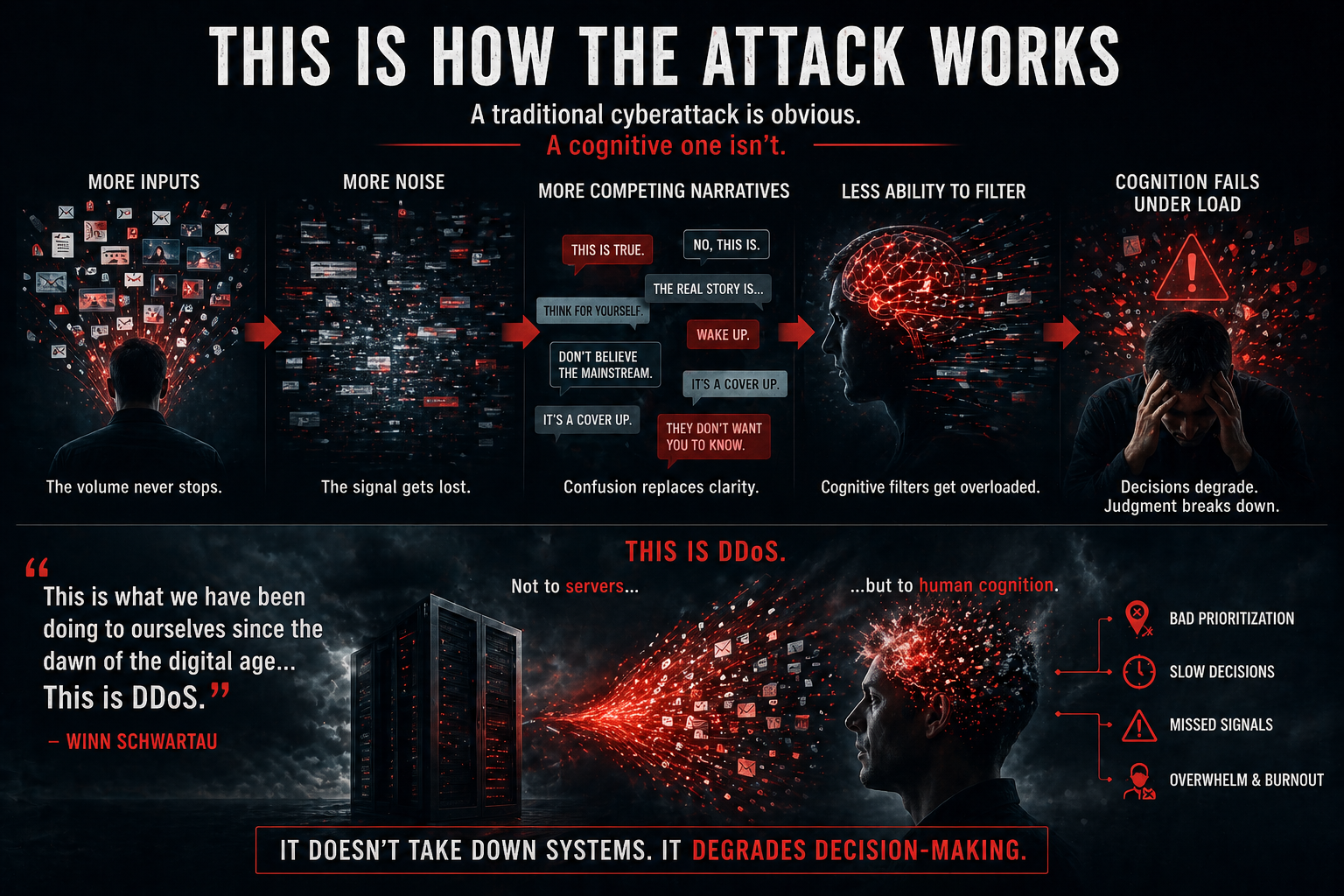
Security conversations around AI tend to fixate on misinformation, deepfakes, and disinformation. Schwartau says the biggest problem we're up against is too much information. Humans can’t process everything coming at them. When they try, they break down.
“If you critically think everything that’s coming at you, you are in mental DDoS mode. You cannot do it,” Schwartau says.
That’s the condition attackers or even just the modern information ecosystem don’t need to exploit directly. They just need to let it happen.
The real failure is in filtering
Security teams talk about detection, response, and analysis. Schwartau inserts a missing step before all of that:
“There’s a step before [critical thinking]… critical ignoring.”
If everything gets through, nothing gets processed correctly. That’s true for networks and also for people, he says:
“You don’t need to know it all… if it all comes into your system, you’re going to lose.”
The battlefield has shifted
Schwartau’s career has tracked the evolution of the problem:
- Infrastructure attacks
- Time-based security
- Now: cognitive security
The throughline is that attackers go where leverage is highest. Right now, that’s not infrastructure but perception. In a world of constant input, that filtering system is under strain.
It’s already happening at every level
Schwartau breaks the “Cognitive Pearl Harbor” idea into three layers:
- Individual: belief systems shaped by overwhelming input
- Enterprise: decisions made under information overload
- Societal: entire groups aligning around narratives
At each level, nothing “breaks” in the traditional sense. The system keeps running. It just makes worse decisions.
The uncomfortable part
Security has always assumed a boundary: We defend systems. Users are part of the environment.
That boundary is gone. Cognition itself is now part of the system and part of the attack surface. And unlike infrastructure, it has hard limits.
That’s the constraint everything else has to work within.
What it means to you
If a cognitive Pearl Harbor has already happened, you won’t find it in logs. You’ll see it in:
- bad prioritization
- slow decisions
- missed signals
- teams overwhelmed by noise
“You don’t have time… you don’t have the bandwidth… you don’t have the capability,” Schwartau says.
The job isn’t just to detect more. It’s to filter better, before thinking even begins. Because if the system is overloaded, it doesn’t matter what tools you have. You’ve already lost the loop.