CYBR.SEC.Media 2.0: How CYBR.SEC.Community Is Building a More Human Cybersecurity Media Platform
The new version of CYBR.SEC.Media puts community voices, practitioner insight, podcasts, videos, and visual storytelling front and center.
The new version of CYBR.SEC.Media puts community voices, practitioner insight, podcasts, videos, and visual storytelling front and center.
From SOC burnout and alert fatigue to resilience and psychological sustainability, these five cybersecurity mental health articles helped shape one of the industry’s most important conversations.

But it might be your company’s problem.

What a nonprofit collects, captures, manages, and is responsible for protecting isn't uniform. And in many cases, the sensitivity of that data maps directly back to their unique mission in ways that should fundamentally shape how we approach security for these organizations.

Here are several organizations and initiatives dedicated to mental health for security professionals.

Cybersecurity is more than keyboards, dashboards, and job titles. At CYBR.SEC.Community, we’re researching the broader ecosystem of roles, skills, and people that make this community work—and why that broader view should encourage more people to find their place in it.

Feeling the mental strain that is often part of working in cybersecurity? I'll admit that I am. But we're not alone, and we have allies to see us through. This post celebrates Mental Health Hackers. We will spotlight other great efforts in the community throughout the month.

Cybersecurity treats nonprofits as a single category, despite vast differences in mission, data sensitivity, and risk. From animal shelters to domestic violence services to hospitals, each faces a distinct threat landscape.

Here are just a few of the voices who inject cutting-edge insights into the community we are building.

Security pros often don’t understand why their business won’t accept certain types of solutions. Thus, they can’t articulate those problems to vendors. If both sides can't grasp why existing solutions aren’t organizationally viable, they stand no chance at building better solutions that are viable.
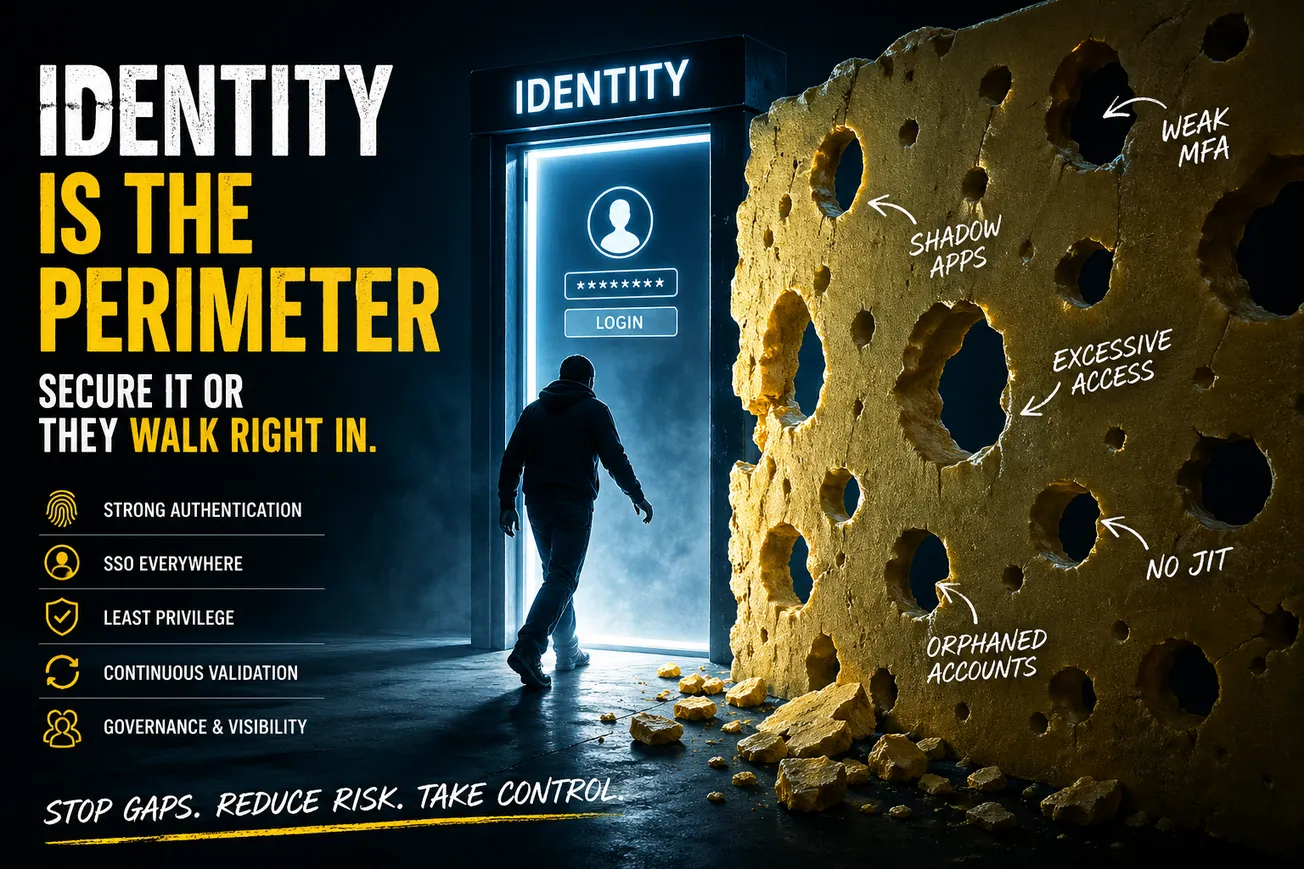
Dave Lewis, Global Advisory CISO at 1Password, says if you treat identity as your perimeter, you stop caring about where traffic comes from and start caring about who is asking for access, how they proved it, and what they are allowed to do. Here's how to go about it.

Adrian Sanabria built "Destroyed By Breach" to cut through cybersecurity myth-making, and what he found is more uncomfortable than the fear-driven narrative the industry often sells.

The hype over Anthropic Mythos and AI in general has been super-heated. The cybersecurity voices who calmly unpack the details are the ones to follow. Here are some examples.

Five people worth following – not just because they’re speaking at CYBR.HAK.CON, but because they represent what this community is supposed to be.

Cybersecurity is not something that is necessarily intuitive for the vast majority of people. That’s where the problems creep into scope. Much like walking in the dark towards the kitchen, there is the ever-present danger of a piece of Lego lurking in the carpet.

It’s been quite a long time since we stopped naming servers like pets, instead treating them more like cattle farms. But AI has brought cute naming back to the forefront.