One of the best things about this job is how it's based around a community that includes many close friends – people I've known and worked with over the past 22 years in cybersecurity. This week's #FollowFriday celebrates five of them.
Dave Lewis

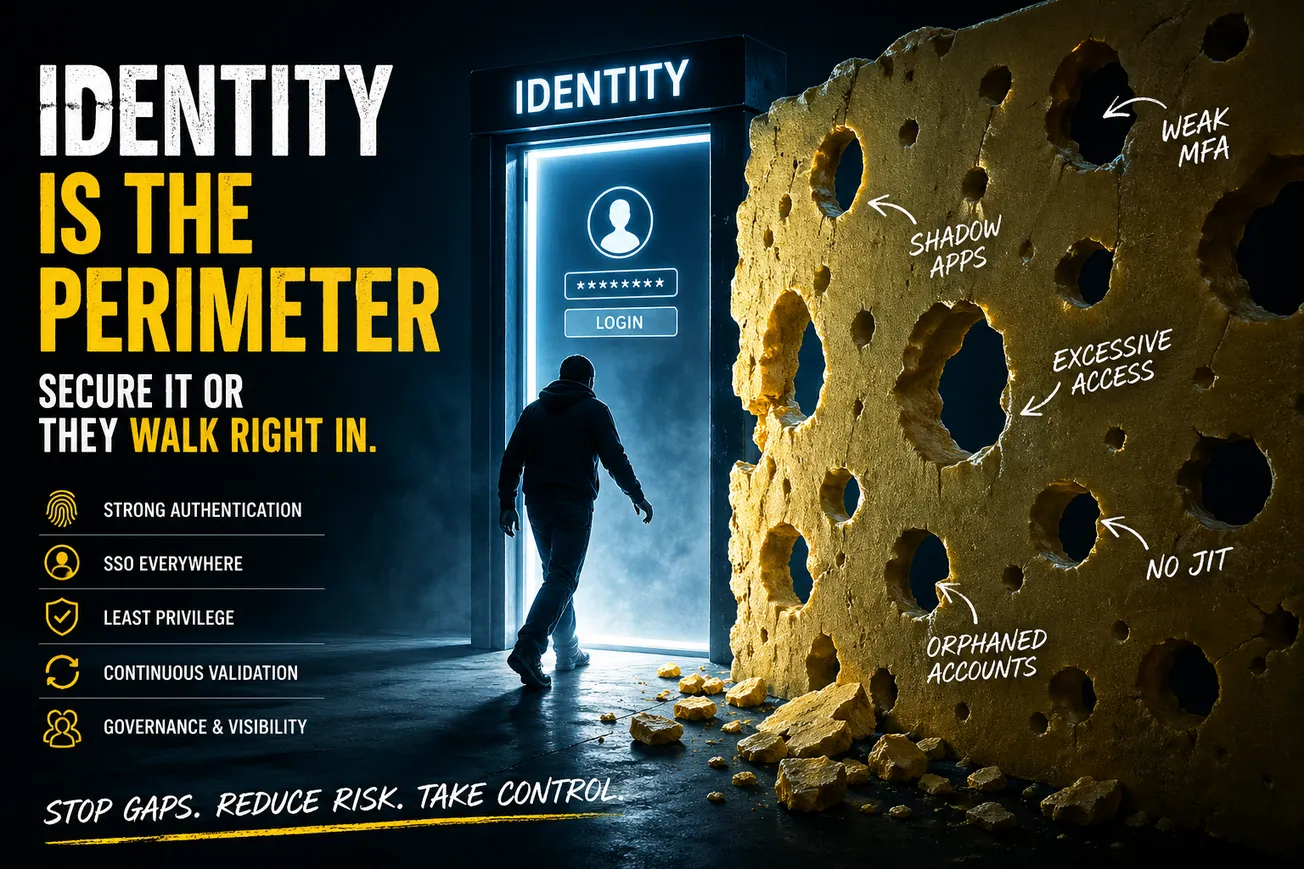
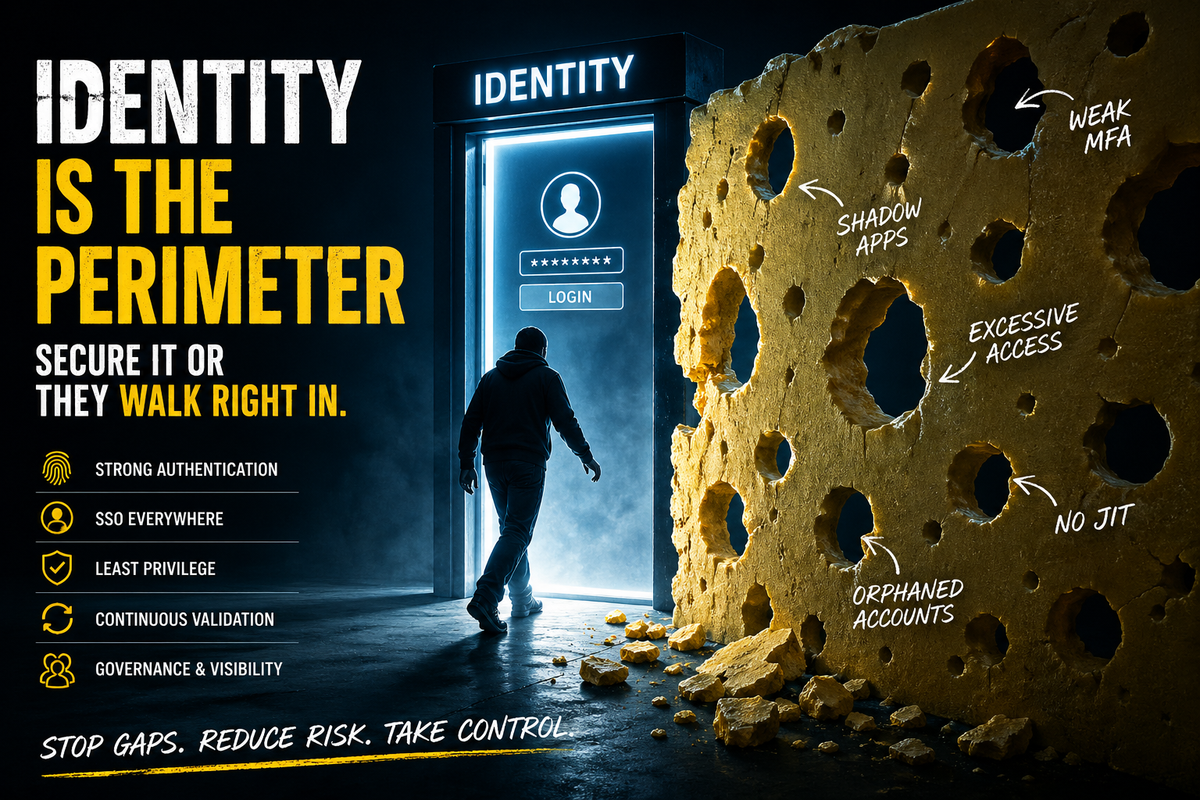
Dave and I worked together at Akamai (for the next guy on this list) and have been friends forever. He travels the world regularly, sharing his insight with countless security practitioners. I first discovered him via his LiquidMatrix Security Digest and as a reporter I'd call on him regularly for story quotes. He is currently a Global Advisory CISO for 1Password and has contributed some great identity-focused content to our community.
Contributions to CYBR.SEC.Community:


Where to follow:
- LiquidMatrix: https://www.liquidmatrix.org/blog/
- Chasing Entropy podcast: https://feeds.buzzsprout.com/2497520.rss
- X: https://x.com/gattaca
- LinkedIn: https://www.linkedin.com/in/gattaca/
Andy Ellis

I worked for Andy for 3 years, during his long reign as CSO of Akamai. He is the go-to guy for insights on CISO leadership and since Akamai his focus has been on helping individuals and companies launch. I'm just one of the people over the years who have benefitted from opportunities he put in front of me.
Contributions to CYBR.SEC.Community:


Where to follow:
- Duha (his consultancy): https://www.duha.co/
- How to CISO: https://www.howtociso.com/author/andy/
- His Book: https://www.amazon.com/1-Leadership-Master-Improvements-Leaders/dp/0306830817
- X: https://x.com/csoandy
- LinkedIn: https://www.linkedin.com/in/csoandy/
Kelley Misata

Kelley is founder of SightLine Security, an organization that helps nonprofits manage the challenges of cybersecurity. Dave and I are both proud members of her advisory board and she is gearing up to do some frequent blogging on this site. Her appearance on CYBR.SEC.CAST is one of the most popular episodes to date. She also has a powerful origin story that inspires us.
Contributions to CYBR.SEC.Community:


Where to follow:
- Sightline Security: https://sightlinesecurity.org/
- LinkedIn: https://www.linkedin.com/in/kelley-misata-ph-d-38475636/
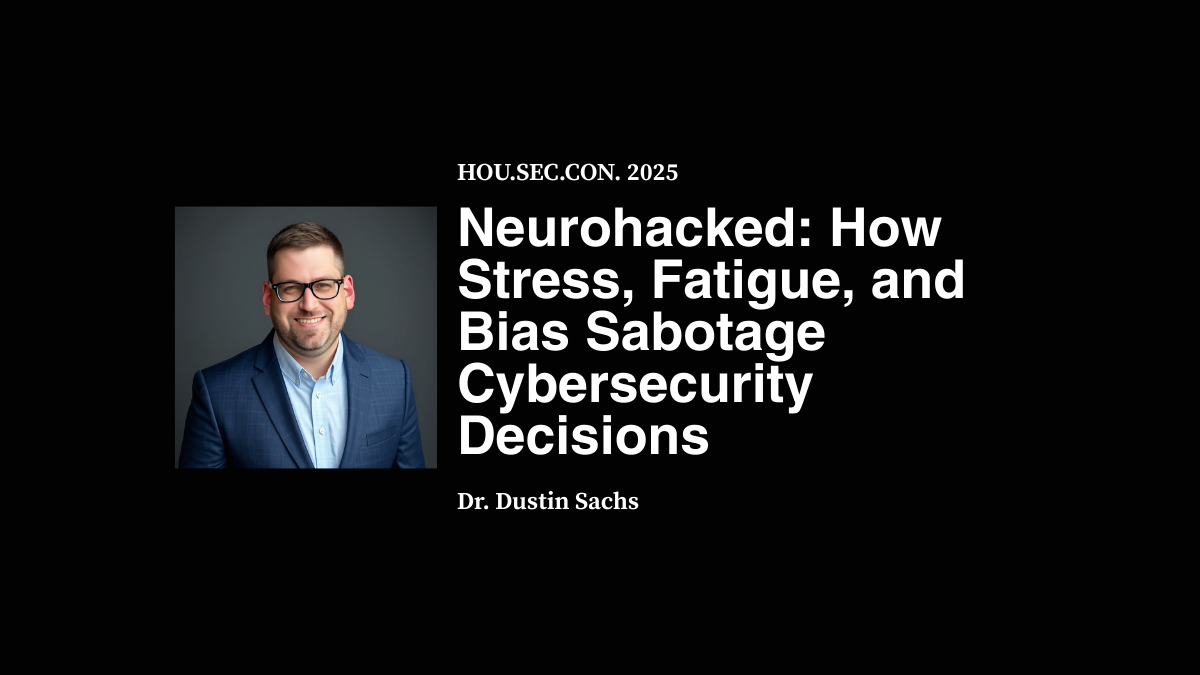
Dustin Sachs

I worked with Dustin at CyberRisk Alliance and he is now a regular contributor to our community. His experience is such that he already made the #FollowFriday list once before. He is currently building PsyberCog Labs, which integrates behavioral science with enterprise-grade cybersecurity so policy becomes practice and the secure choice becomes the easy choice, every day, at scale. You'll be seeing a lot of him on this site.
Contributions to CYBR.SEC.Community:


Where to follow:
- Psybercog Labs: https://www.psybercog.com
- His book: https://www.amazon.com/Behavioral-Insights-Cybersecurity-Security-Leadership-ebook/dp/B0FCFXMNL9?ref_=ast_author_mpb
- LinedIn: https://www.linkedin.com/in/dustinsachs/
Robert "RSnake" Hansen

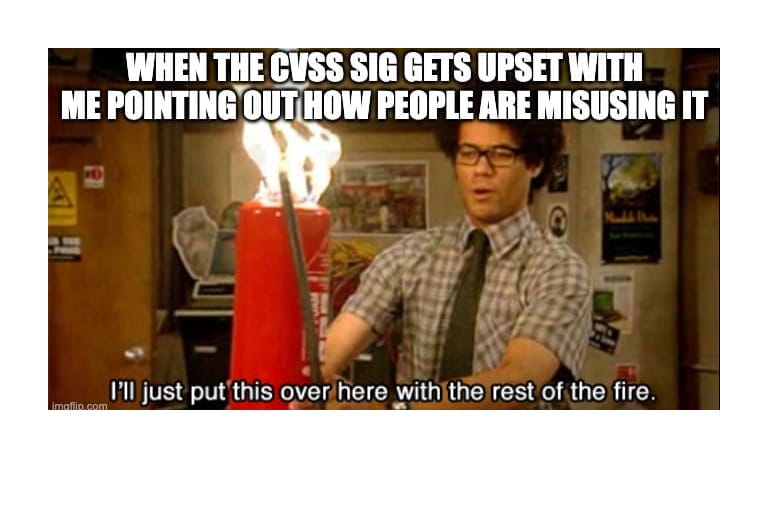
Robert is CTO at Root Evidence and Managing Director at Grossman Ventures. He has been one of our most popular keynoters and is not afraid to challenge some of the industry's sacred cow lines of thinking. The keynote he gave at HOU.SEC.CON certainly touched a nerve with the audience.
Contributions to CYBR.SEC.Community:

Where to follow:
- Root Evidence: https://www.rootevidence.com/
- Grossman Ventures: https://grossman.vc
- The RSnake Show: https://rsnake.com/
- His latest book: https://www.amazon.com/AIs-Best-Friend-Robert-Hansen-ebook/dp/B0CWDJCVHT?ref_=ast_author_mpb
- X: https://x.com/RSnake
- LinkedIn: https://www.linkedin.com/in/roberthansen3/
More FollowFriday: