Presenters:
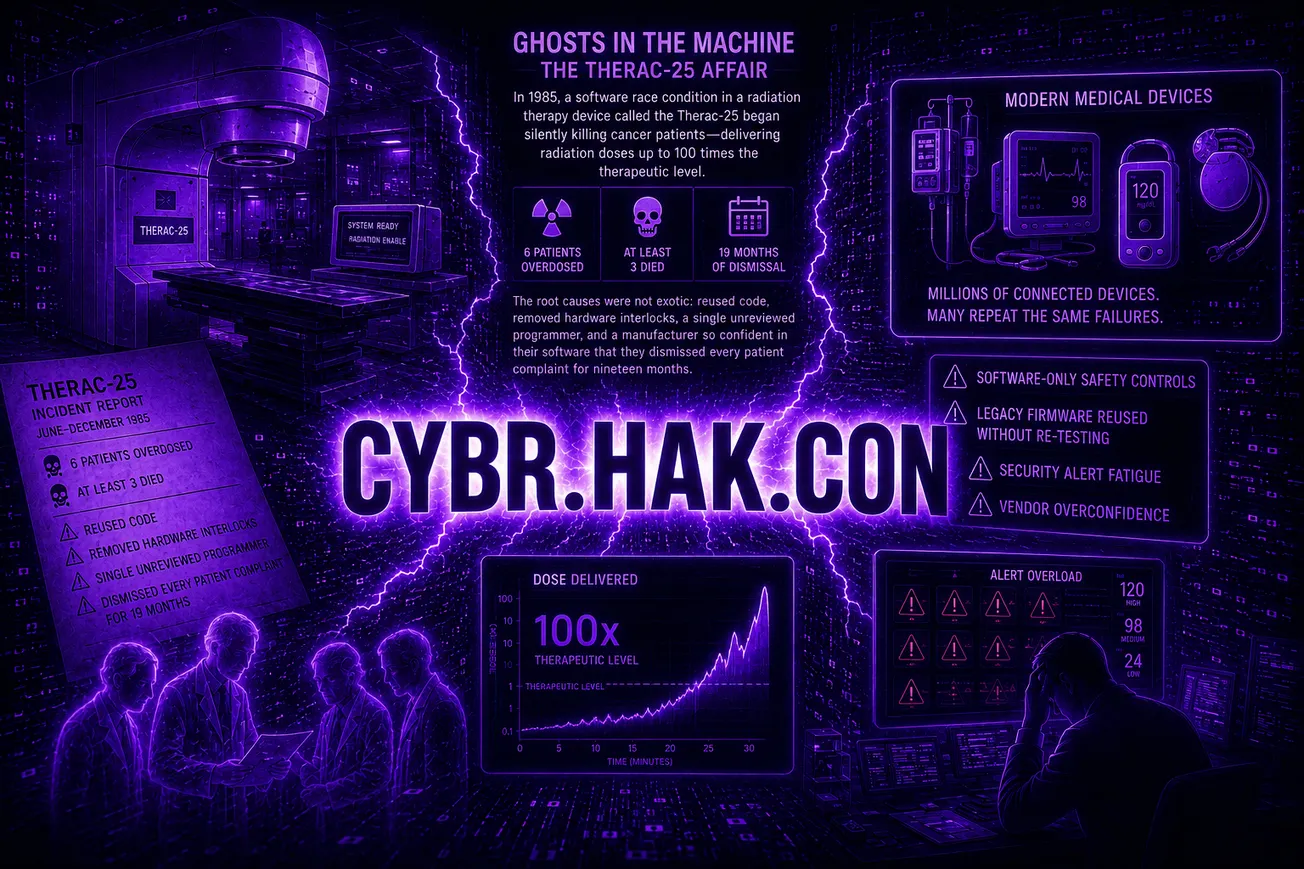
This session focuses on how defenders consistently underestimate how attackers actually operate in real environments — especially in OT and critical infrastructure. The result: defenses are built for theory, while attacks succeed in practice.
Key takeaways
- Defenders design for ideal conditions
- Clean architectures
- Proper segmentation
- Fully implemented controls
- Reality: none of that exists at scale
- Attackers exploit the messy middle
- Misconfigurations
- Workarounds and exceptions
- Legacy systems glued together over time
- The “temporary” fixes that became permanent
- Security models don’t match operations
- Playbooks assume visibility and control that teams don’t actually have
- Monitoring doesn’t reflect real workflows
- Response plans break down under real-world constraints
- The environment is the vulnerability
- It’s not just individual flaws
- It’s how systems are interconnected and operated day to day
- Risk lives in the gaps between intended design and actual use
- You have to test reality, not assumptions
- Hands-on validation in real environments
- Red/blue/purple teaming that reflects operational constraints
- Continuous testing of how systems actually behave