Since this most recent start of hostilities between the US, Israel and Iran, the cyber conflict has continued to escalate with direct Iranian attacks on data centers, the compromising of US and Israel critical infrastructure, and even the “gig economy” has been impacted.
On March 2, Amazon Web Services confirmed that two of its data centers in the United Arab Emirates were struck and a third facility in Bahrain sustained damage from a nearby strike. The attacks caused "structural damage, disrupted power delivery to our infrastructure, and in some cases required fire suppression activities that resulted in additional water damage," AWS stated in its service dashboard update, as reported by the Associated Press.
While AWS did not identify the source of the strikes in its statement. Reuters and CNBC subsequently reported the attacks were attributed to Iranian drone strikes. AWS urged customers to activate disaster recovery plans and migrate Middle East workloads to alternate regions immediately.
More on the Middle East conflict:
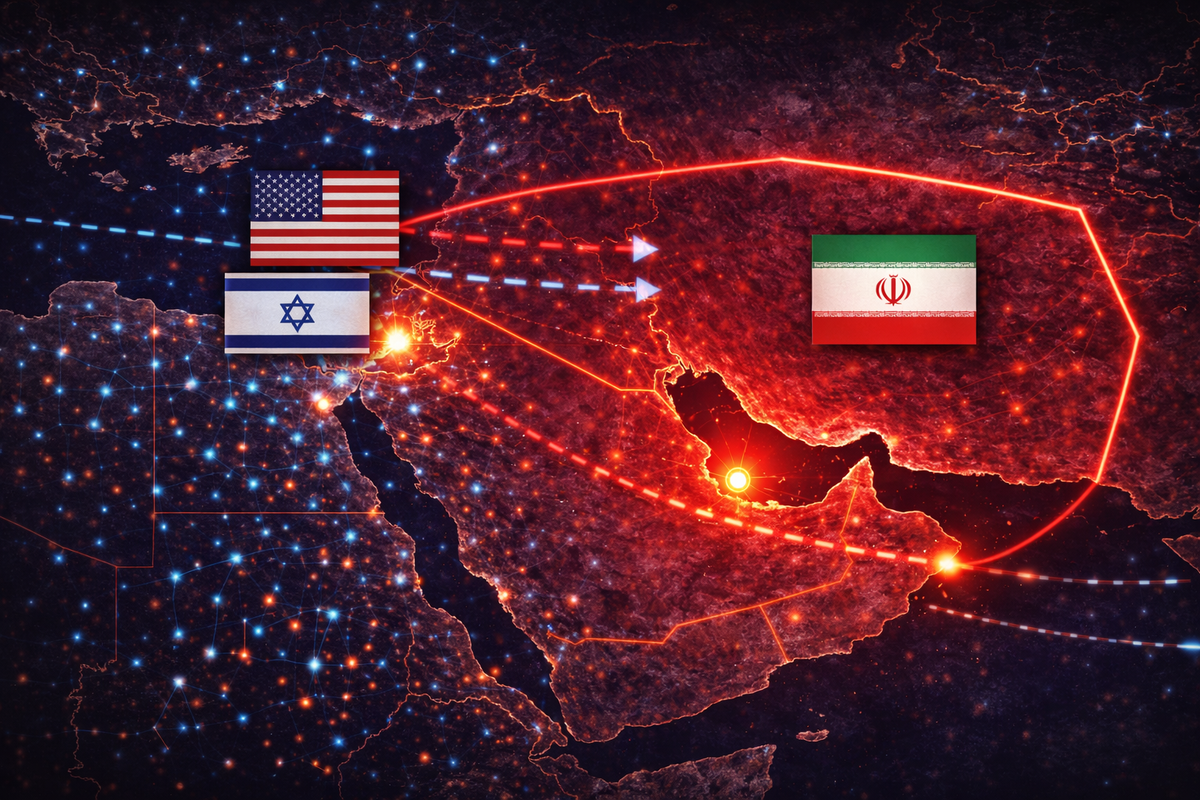


Iran's Islamic Revolutionary Guard Corps (IRGC) claimed responsibility through state-affiliated Fars News Agency, stating the Bahrain facility was targeted specifically because AWS hosts U.S. military and intelligence workloads there. The strikes mark what experts are calling the first instance of American big tech companies being directly targeted in a military operation, and raise significant questions about the security posture of cloud infrastructure concentrated in conflict zones.
Amazon and Google hold a combined $1.2 billion contract with the Israeli government to provide cloud services and AI capabilities to entities including the Israel Defense Forces, according to Bloomberg reporting cited by Anadolu Agency: a relationship the IRGC has used publicly to justify commercial cloud infrastructure as a legitimate military target.
MOIS Pre-Positioned Inside U.S. Networks Before First Strike
Iran's Ministry of Intelligence and Security (MOIS) had already successfully infiltrated the networks of at least five U.S. and allied organizations since early February, including a defense and aerospace software supplier, a U.S. bank, and a U.S. airport, according to research published March 5 by Broadcom's Symantec Threat Hunter Team and Carbon Black. The campaign, attributed to the MOIS-linked APT group MuddyWater (also tracked as Seedworm, Temp Zagros, and Static Kitten), is ongoing and predates the Feb. 28 U.S.-Israel military strikes on Iran, suggesting it was part of a deliberate pre-positioning strategy.
"Activity associated with Iranian APT group Seedworm has been spotted on the networks of multiple U.S. companies," Broadcom's Symantec wrote in its March 5 advisory. The activity began in February 2026 and has continued in recent days.
Two New Weapons: Dindoor and Fakeset
The intrusions introduced two previously undocumented malware families. Dindoor (Trojan.Dindoor), built on the Deno JavaScript runtime, was deployed against the defense supplier and the U.S. bank, providing persistent access and the capability for arbitrary command execution and data exfiltration. A separate Python-based backdoor, Fakeset (Trojan.Fakeset), was found on U.S. airport and NGO networks, hosted on Backblaze cloud storage servers. Both tools were signed with the "Donald Gay" or “Amy Cherne” digital certificate, previously linked to MuddyWater malware, providing high-confidence attribution to the MOIS-subordinate group, according to Symantec's Threat Hunter Team.
Researchers also observed an attempt to exfiltrate data from the targeted defense supplier using Rclone to a Wasabi Technologies cloud storage bucket. Whether the transfer was completed before disruption remains unconfirmed.
The targeted software firm is particularly significant: it operates an Israeli subsidiary, making it a dual-use intelligence target, simultaneous access to U.S. defense sector intellectual property and Israeli military-adjacent networks from a single foothold.
The Broader Cyberwar, Hacktivist Landscape
MuddyWater's verified intrusions represent only the most technically sophisticated tier of a much wider offensive. Palo Alto Networks' Unit 42 reported on March 2 that Iran's internet connectivity collapsed to between 1 and 4 percent following U.S.-Israel strikes — temporarily suppressing coordinated nation-state operations inside Iran — but simultaneously activating an estimated 60 Iran-aligned hacktivist groups operating outside Iranian borders. Many operate under a newly formed "Electronic Operations Room" established on Feb. 28, 2026.
Those groups include Handala Hack, tied to MOIS, which claimed disruption of Jordanian fuel distribution and access to an Israeli energy company; the FAD Team (Fatimiyoun), which claimed unauthorized access to Israeli SCADA/PLC systems; the 313 Team, which claimed to have taken down Kuwaiti Armed Forces and Ministry of Defense websites; and DieNet, which claimed DDoS attacks on U.S. critical infrastructure. As of March 9, Iranian-linked actors have also been observed probing U.S. state and local government networks, according to a report from News4Hackers citing intelligence briefings.
On March 9, UK officials expressed concern over Iranian intelligence using Telegram to recruit "gig-economy" spies across Europe, according to reporting by Richard Holmes. The development points to Iran expanding its human intelligence collection operations in parallel with its cyber campaign, using encrypted messaging platforms to recruit ad-hoc operatives with no formal intelligence background.
Also on March 9, pro-Russian group NoName057(16) claimed distributed denial-of-service attacks against Israeli political parties and defense firm Elbit Systems — a sign that Russia-aligned actors are actively exploiting the conflict to compound pressure on Israeli targets. That claim has not been independently verified. Separately, Handala claimed to have wiped Israeli military weather servers and intercepted Jerusalem urban security camera feeds; that claim also remains unverified.
Cyber Islamic Resistance (Team 313) has claimed a series of website defacements against regional targets over the past week. Those include the official website of the Kurdish Peshmerga special forces — an operation the group explicitly framed as a warning against supporting anti-regime Kurdish factions — along with a Saudi medical care application (smcc[.]sa) and the Saudi University of Business and Technology (staging[.]ubt[.]edu[.]sa). None of these claims have been independently verified.
There’s a caveat that applies across all hacktivist activity: the Foundation for Defense of Democracies assessed on March 4 that Iran's proxy hacktivist groups routinely exaggerate impact for psychological effect and have frequently been unable to substantiate Telegram claims with technical evidence. The MuddyWater intrusions, by contrast, are confirmed.
The AI Accelerant
U.S. cybersecurity firms warn that Iranian actors are now employing AI-assisted tooling to compress attack timelines. According to CloudSEK's March 5 ICS/OT threat landscape assessment, Iranian-aligned groups are using AI to automate Shodan and Censys queries, identifying internet-exposed industrial control systems in minutes — no exploitation skill required when default credentials remain unchanged. The report flagged that many Unitronics PLCs remain internet-facing with the default PIN of 1111, making them trivially accessible.
Broadcom's Symantec confirmed that MuddyWater has now expanded beyond its traditional telecommunications and government targets into critical infrastructure, energy, transport, healthcare, and defense sectors. "Researchers warn that Iranian-aligned actors may escalate with DDoS attacks, defacements, credential theft, leaks, and potentially destructive operations," Symantec stated.
As we covered earlier, the intrusions arrive at a particularly precarious moment for U.S. cyber defenses. The Cybersecurity and Infrastructure Security Agency (CISA), the lead federal body for critical infrastructure incident response is operating at reduced capacity due to a partial government shutdown, employee furloughs, and an ongoing leadership reshuffle, as CNBC reported March 3. The FBI issued a separate reminder on March 3 that critical infrastructure operators must implement mitigations from its June 2025 Iran advisory, warning that Iranian actors specifically target internet-connected OT systems and ICS devices using default passwords and unpatched software.
Immediate Risk Assessment and Recommended Actions
Palo Alto Networks' Unit 42 assesses that the current threat posture combines low-to-medium impact hacktivist operations with a credible and ongoing nation-state espionage campaign that could transition to destructive operations. The highest-risk sectors are energy and fuel distribution, water utilities, the defense industrial base, financial services, and state and local government.
Unit 42 and the FBI recommend security teams take the following actions immediately:
· Remove all ICS and OT interfaces from public internet exposure. There is no operational justification for PLCs or SCADA interfaces to be internet-facing.
· Change all default credentials on industrial devices — Unitronics, Siemens, Schneider Electric, and Rockwell Automation devices with factory-default credentials represent the lowest-effort path to OT compromise.
· Deploy IoCs for Dindoor and Fakeset now. File hashes and certificate indicators have been published by Broadcom's Symantec and are available in the Broadcom Security Center advisory.
· Monitor for unauthorized Rclone and cloud sync activity targeting Wasabi, Backblaze, or other non-enterprise cloud storage — MuddyWater's confirmed exfiltration method.
· Enforce phishing-resistant MFA on all remote access — VPNs, email portals, and cloud consoles — as credential-based initial access remains MuddyWater's primary entry vector.
· Validate offline backup integrity. Iranian wiper malware specifically targets network-connected backup systems; at least one air-gapped copy is essential.
· Engage your sector ISAC for current IOC feeds. Given CISA's reduced operational capacity, sector-specific intelligence sharing has never been more important.
These are all a rapidly evolving set of stories, CYBR.SEC.Media editor-in-chief Bill Brenner has gathered a list of resources to keep up with the most recent developments.