
Iranian Attack on Stryker Brings BYOD Dangers Back to Center Stage
The bring-your-own-device (BYOD) dimension carries implications well beyond Stryker.

The bring-your-own-device (BYOD) dimension carries implications well beyond Stryker.

While Iranian drones were taking out Amazon's data centers in the Gulf, Tehran's hackers were already inside U.S. banks, airports, and defense networks — and they got there weeks before the first missile flew.

This list -- to be updated regularly -- contains sites that are ideal for those tracking cyber activity surrounding the US-Israel-Iran conflict.

As Iran's cyber forces regroup after the most devastating military strikes in the Islamic Republic's history, the U.S. agency built to defend the nation's critical infrastructure is operating with a skeleton crew, gutted leadership, and a funding crisis — at precisely the moment it is needed most.

The escalating conflict with Iran underscores how the once-clear boundary between cyber and kinetic warfare has collapsed, forcing organizations to rethink cybersecurity as inseparable from physical and geopolitical risk.
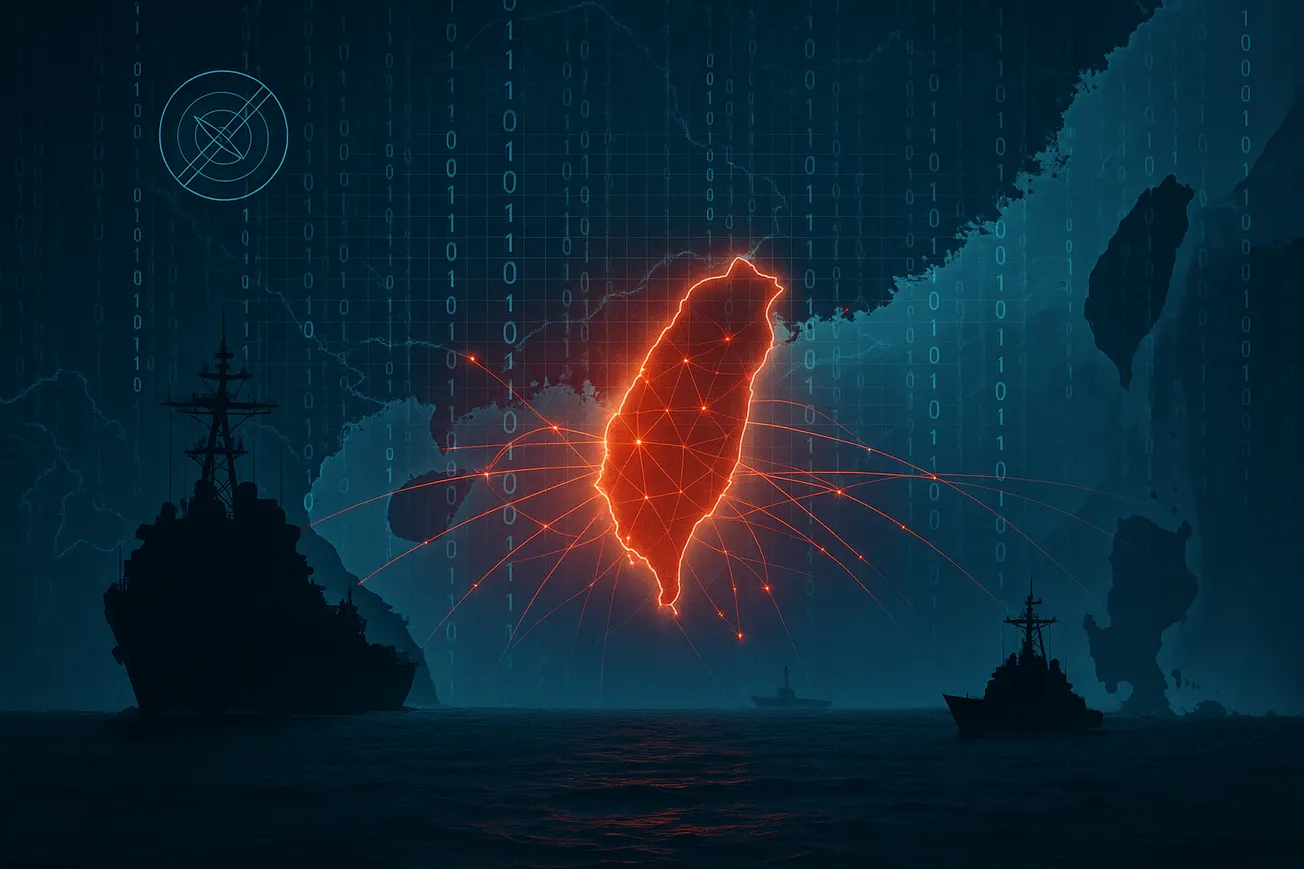
In a potential hot conflict over Taiwan sovereignty, cyber operations would be at the forefront, and aimed at slowing the U.S. military response, targeting military logistics systems, cloud-based sustainment platforms, naval communications, and intelligence, surveillance, and reconnaissance systems.