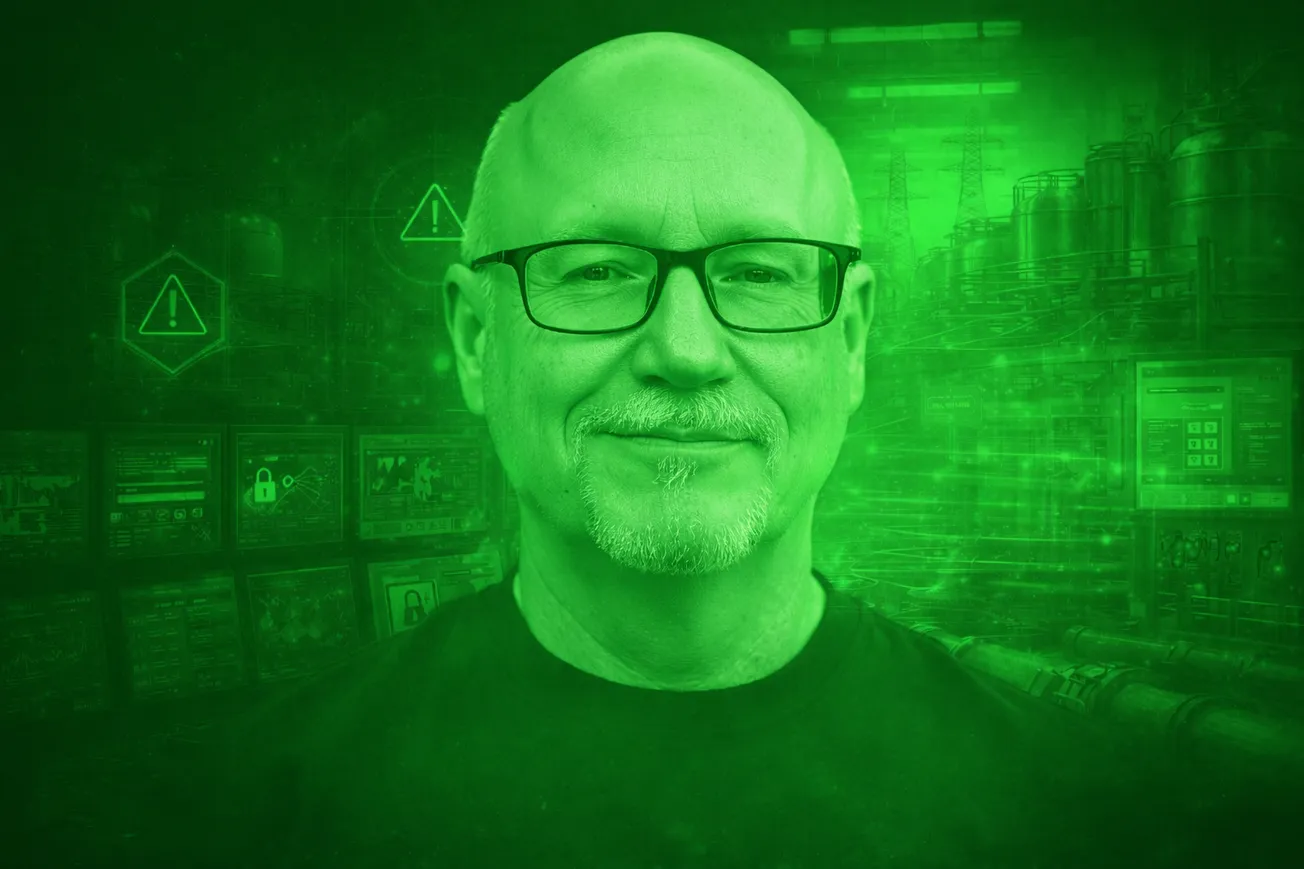
As industrial environments become more connected — and more exposed — the gap between IT security and operational technology (OT) is no longer a theoretical problem, but a real-world risk. That’s the gap Mike Holcomb is aiming to close with his hands-on training session at OT.SEC.CON, held March 31 in Houston.

Holcomb, founder of UtilSec and a leading voice in OT/ICS cybersecurity, designed the training as a one-day accelerated bootcamp built from his widely followed 26-hour online course.
This is an updated, practical immersion into how industrial systems function and how attackers and defenders interact with them. He discussed the training and more during a recent CYBR.SEC.CON (renamed OT.SEC.CAST for this occasion) podcast episode:

Bridging Two Worlds That Rarely Meet
At its core, Holcomb’s training is about convergence. Most attendees come from IT security backgrounds — people who understand networking, TCP/IP, and enterprise risk. Others come from engineering and plant operations — those who understand PLCs, control systems, and how production environments actually run.
The problem? These groups rarely speak the same language.
Holcomb’s approach brings them together in a shared learning environment, walking through how industrial systems operate, how components interact, and where security breaks down. It’s not just about identifying vulnerabilities—it’s about understanding the system well enough to anticipate them.
That’s critical, because as Holcomb emphasizes, there simply aren’t enough OT-native security professionals to defend today’s environments. The only path forward is collaboration.
From Theory to Hands-On Reality
This isn’t a lecture-heavy session. Participants move through labs and exercises in virtualized environments, exploring OT systems from both attacker and defender perspectives. The goal is to shift mindset — from abstract security controls to real-world consequences.
The emphasis is on learning by doing. Course materials, including slides, scripts, and tools, are provided for continued use after the session.
Designed for Those New to OT—But Serious About It
Holcomb intentionally designed the training for those “new or new-ish” to OT security. That includes:
- IT security professionals looking to expand into industrial environments
- Engineers and operators seeking to understand cybersecurity risks
- Anyone responsible for systems where digital compromise can lead to physical impact
A basic understanding of networking helps, but curiosity and willingness to learn matter more.
The session also offers CPE credits, with a short post-training quiz and certification—making it practical not just from a skills standpoint, but for professional development as well.
Why This Training Matters Now
The timing of this training, immediately ahead of OT.SEC.CON, is intentional.
Holcomb’s session sets the foundation for the broader conversations happening at the conference: how IT and OT teams collaborate, how modern threats exploit industrial environments, and why traditional models no longer apply.
Holcomb’s training doesn’t just teach tools or frameworks. It teaches perspective: how to see the plant, the network, and the threat landscape as one interconnected system.