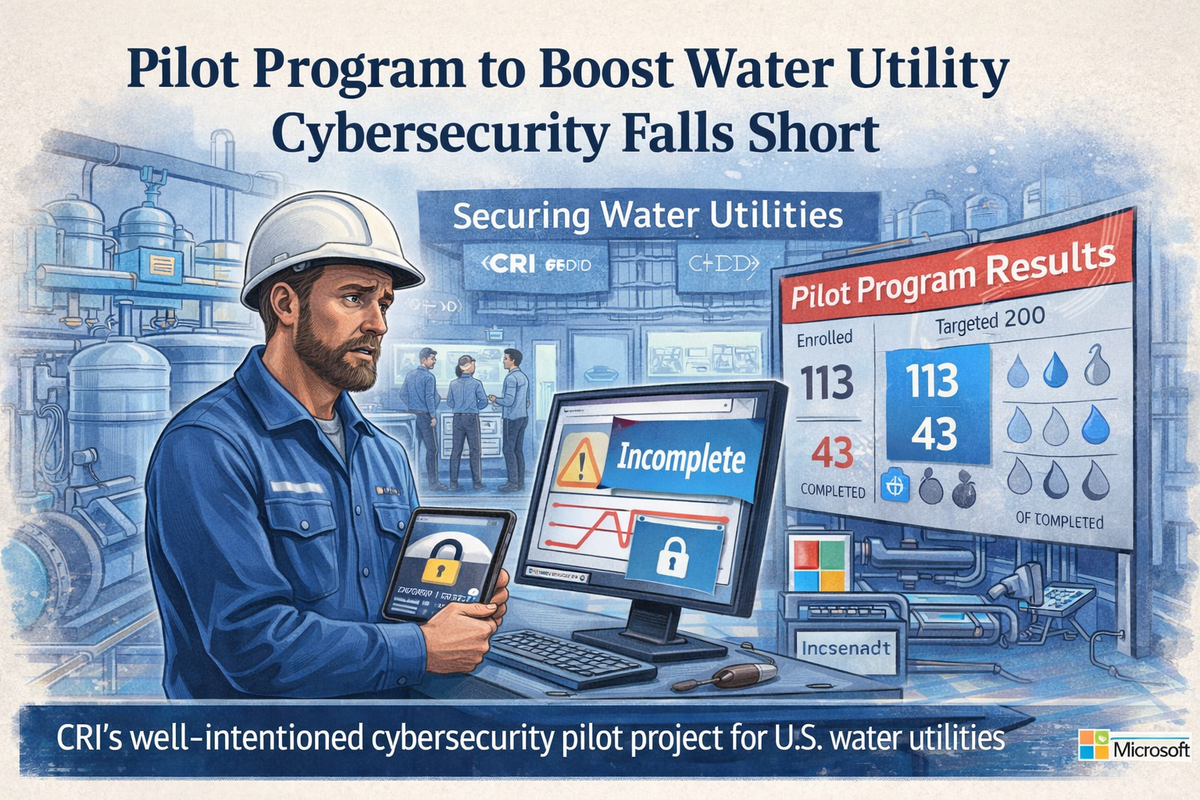
In 2023, a well-funded, well-intentioned initiative set out to improve cybersecurity across U.S. water utilities. Backed by major institutions and designed to help one of the most vulnerable sectors in critical infrastructure, it had all the right ingredients — visibility, funding, and urgency.
The results tell a different story: Out of 113 utilities that enrolled, only 43 completed the program.
The lack of success reflects a deeper truth the cybersecurity industry has been slow to confront: you cannot solve operational technology (OT) and critical infrastructure risk with the usual mix of awareness campaigns, generic training, or IT-first thinking. These environments are constrained, understaffed, and deeply physical. They require hands-on expertise, sustained investment, and a fundamentally different approach to defense.
And yet, too often, the industry continues to treat them like just another vertical.
Meanwhile, the stakes are rising. Attacks are no longer contained to networks and endpoints. They ripple outward — into hospitals, water systems, transportation, and energy grids. Nation-state and gray-zone actors are increasingly targeting these environments not just for disruption, but for strategic leverage.
From Cybersecurity to Operational Resilience
This is the backdrop for OT.SEC.CON. The event is a recognition that the lines between cyber, physical, and human risk have collapsed.
The agenda brings together leaders working at the intersection of IT, OT, and real-world operations, people who understand that protecting infrastructure means understanding how systems actually function, how failures cascade and how attackers exploit the gaps between teams, technologies, and assumptions.

Sessions span the realities security teams are grappling with right now:
- Securing industrial control systems in environments that can’t simply be patched or taken offline
- Managing risk across IT/OT convergence, where visibility is incomplete and ownership is unclear
- Responding to incidents where cyber events have immediate physical consequences
- Addressing the human layer — operators, engineers, and frontline staff who are now part of the security equation
The speakers themselves reflect this evolution — practitioners, operators, and strategists who aren’t theorizing about risk, but actively managing it in environments where downtime can quickly turn dangerous.
Sessions include:
Why This Matters Now
The failure of programs like the water utility pilot isn’t an outlier. It shows what happens when we underestimate the complexity of critical infrastructure and overestimate the effectiveness of scalable, one-size-fits-all solutions. It shows the limits of awareness without implementation, and strategy without execution.
Most importantly, it shows that we are running out of time to get this right.
Critical infrastructure operators don’t need more dashboards. They need support that meets them where they are: on the plant floor, in aging environments, with limited staff and no margin for error.
That’s the conversation OT.SEC.CON is designed to drive.
More on OT and critical infrastructure security: