
Where to Track Cyber Activity Tied to the US-Israel-Iran Conflict
This list -- to be updated regularly -- contains sites that are ideal for those tracking cyber activity surrounding the US-Israel-Iran conflict.


This list -- to be updated regularly -- contains sites that are ideal for those tracking cyber activity surrounding the US-Israel-Iran conflict.
Five cybersecurity thinkers worth following as they explore how AI is transforming security operations, decision-making, and the future of work for defenders.

They dig into emerging use cases like AI “companions,” virtual girlfriends/boyfriends, grief bots, and even “virtual immortality” where a chatbot continues posting and interacting on social media after someone’s death.

The escalating conflict with Iran underscores how the once-clear boundary between cyber and kinetic warfare has collapsed, forcing organizations to rethink cybersecurity as inseparable from physical and geopolitical risk.

PR people often get a bad rap for their persistence and occasional aggressiveness. But the truth is that they are the connectors, the builders of long-lasting relationships. These five are among the best in cybersecurity.

Where SaaS once scaled predictably with seat-based licensing and human user counts, the rise of machine-to-machine interactions, autonomous agents, and API-driven workflows is collapsing those pricing and value assumptions.
Using AI in the editorial process can be weird. But in an educational way -- whether you're a writer, an image designer or a cybersecurity practitioner.

Here are five people who are taking the lead in making critical infrastructure more resilient in the face of nation-state attacks.

Lazarus-linked threat actors exploit fake recruiter campaigns in an operation ReversingLabs calls “graphalgo,” turning technical job interviews into remote access trojan (RAT) delivery mechanisms that target developers.

Mental health tools for cybersecurity practitioners have become essential in this age of accelerating cyber warfare. Here are five people who are building those tools.

Also: practitioners pushing the community forward, how automation is reshaping defense, and the need for clearer thinking in an increasingly noisy security landscape.
After years of hiatus, my weekly #FollowFriday list is back. There's no better home for it than CYBR.SEC.Media, because we are building a community.
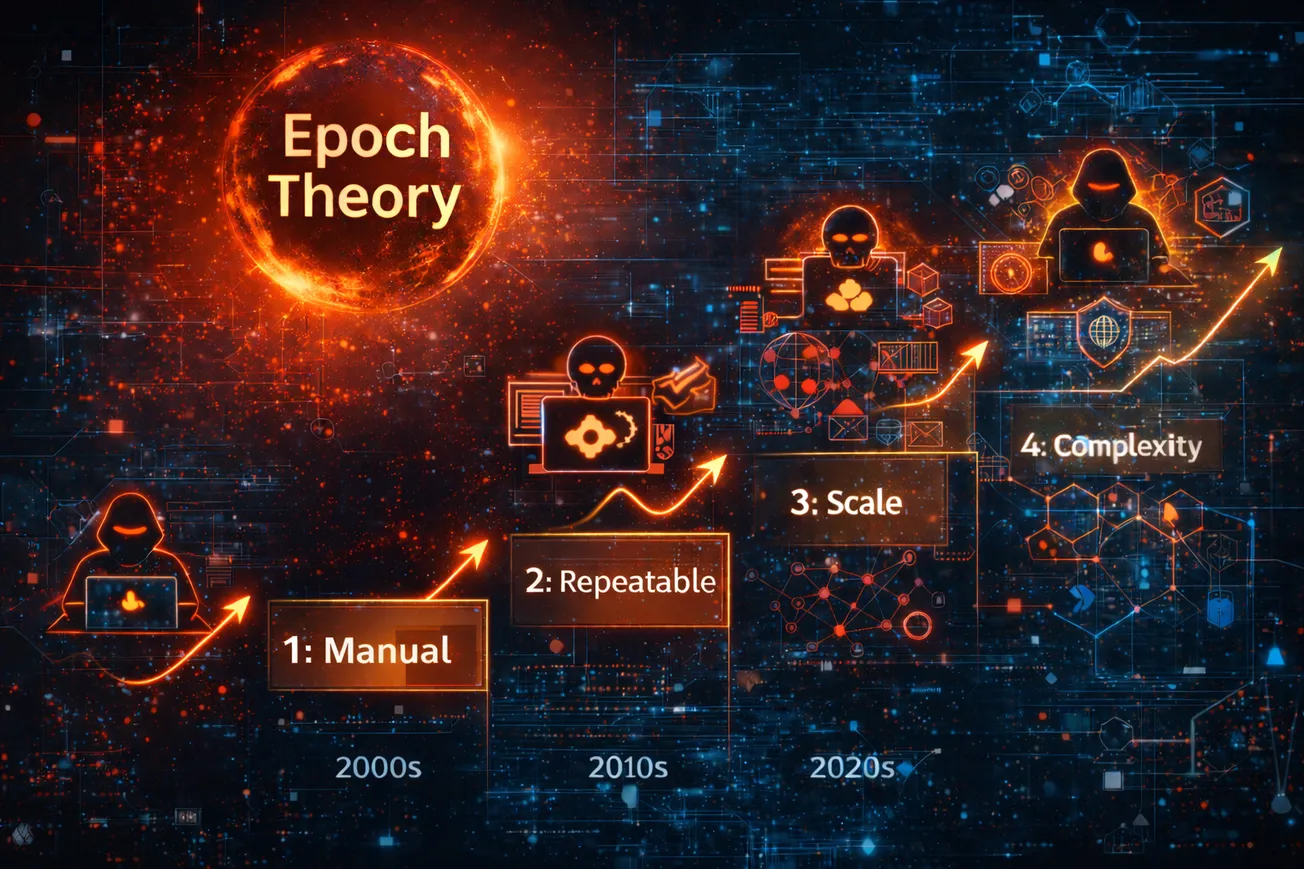
Epoch Theory is Jeremiah Grossman’s framework for understanding how cybersecurity evolves in distinct phases driven by attacker behavior, not defensive intention.
Part of our mission is to be a safe house where cyber travelers can find truth and reason.
Many good individuals, nonprofits, and organizations are trying to address this problem in meaningful ways. But too often, those efforts exist in isolation.